Software to align your content strategies alongside the customer journey
Plan, produce, distribute, and analyze your marketing content —all in one place.
Build seamless customer experiences through content and a unified voice.
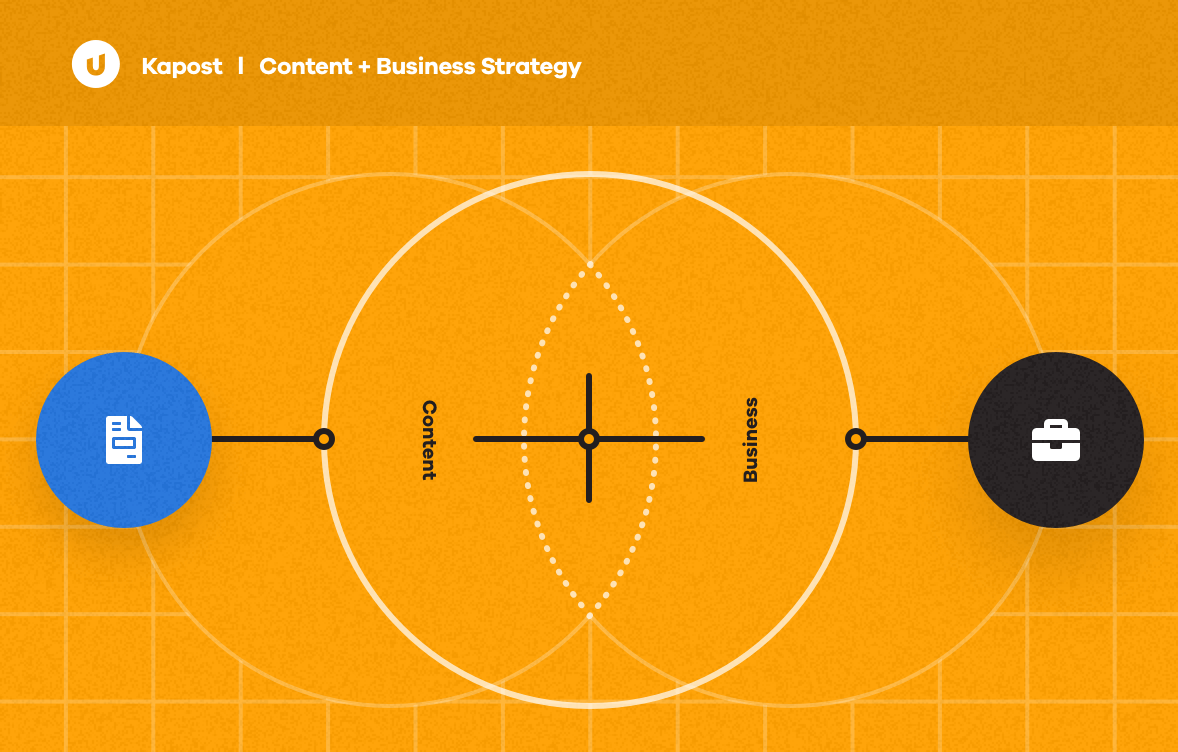
Find the place where content and business strategy can come together.
Define the content that will engage customers at every step of their journey with our powerful content strategy module, Canvas.
- Build and deliver content that meets the business objectives or buying stages specific to the customer journey.
- View resource allocation and prioritize requests to support marketing initiatives across your organization.
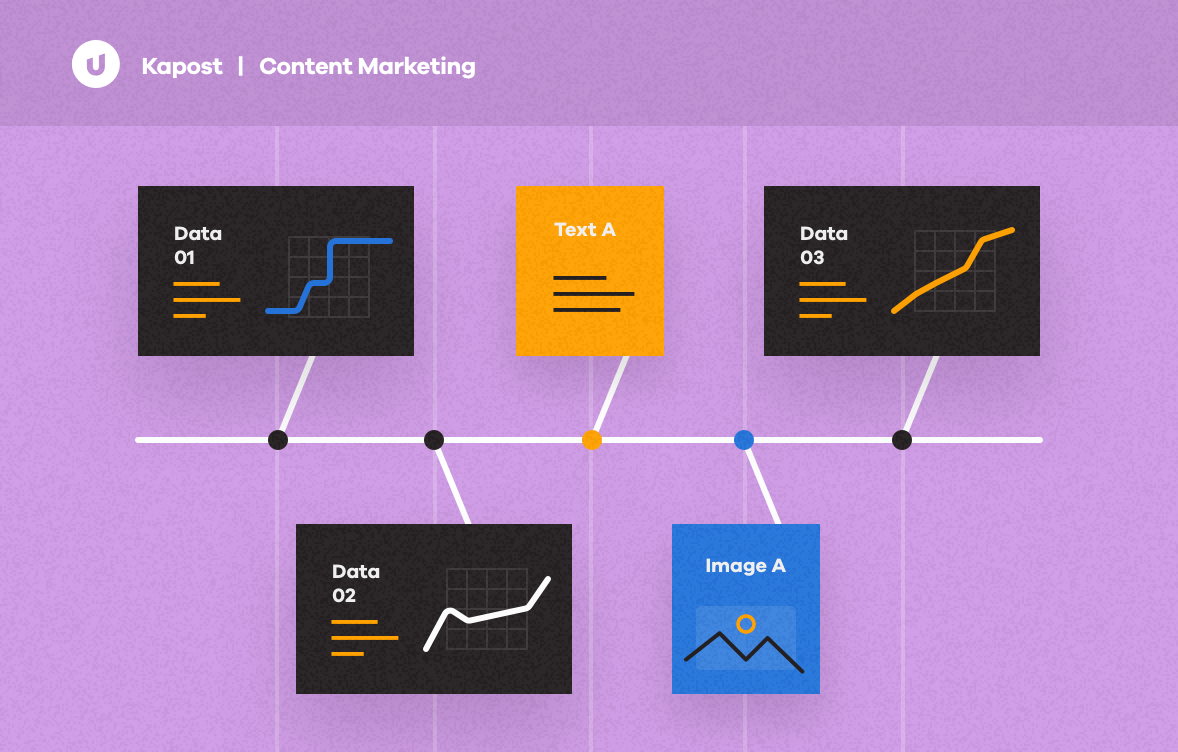
Discover where the real content marketing magic happens.
Plan out initiatives, collaborate with team members, build a content journey, and connect your message to the right audience with Studio. Easy peasy.
- Manage and track every piece of a campaign from content creation through distribution.
- Publish and distribute to multiple platforms from a single tool.
Align marketing with sales.
Empower your sales team with content specific to persona, buying stage, and product line; recommend related content, and connect it all via Salesforce for an on-demand experience with Gallery.
Anchor your strategies to support business objectives and prove ROI.
Analyze content performance and impact via Insights to understand and quantify the value of your content operation.
Build a seamless content stack.
Unite the specialized, but often disconnected, tools used to plan and execute content and campaigns into a single content operation.
You are truly one heck of a company, made up of absolutely the best, most helpful, and most dedicated people in the business. You have a customer for life in me, and I will shout your praises from the rooftop. We still have a long way to go, but it’s all about having people you can trust in your corner.
Customer value fuels our passion
Thousands of customers around the world use Upland Kapost to create and distribute content that supports the buyer journey from awareness to loyalty. Ready to join them?
A key element to your MarTech playground.
We view integrations with an understanding of the foundational processes that underpin your content operations: produce, distribute, and analyze.
As any good marketer knows, there are 100s of platforms and niche solutions that build a strong MarTech stack; these are just a few of our ready-built and premium integrations.
Produce
Marketing Automation
- Marketo
- Eloqua
- Salesforce
Content Development
- Office 365
- Google Drive
Digital Asset Management
- Box
- Adobe Experience Manager
Analyze
Analytics
- Domo
- Google Analytics
Distribute
Content Management Systems
- Hubspot
- Adobe Experience Manager
- Sitecore
- WordPress
- Drupal
CRM Platforms
- Salesforce
Sales Asset Management
- Seismic
- Savo
Social media
- Hootsuite
- Social Studio (Salesforce)
Build and manage a content operation
Upland Kapost gives you everything you need to create consistent, personalized content experiences—at scale.
Plan, analyze, and distribute
- Single location for all approved content and version histories
- Collaborate with peers
- Cross-channel distribution of content calendars
- Granular access settings
Content journey orchestration
- Content alignment to persona, buying stage, interest, and more
- Content pillar ideation to progress the buyer throughout their journey
- Coordinate initiatives with templated workflows
Message unification
- Present a consistent brand message through all content
- Create bundles of related materials for an immersive experience
- Deliver content for sales teams specific to the persona or buying stage
Strategy alignment
- Content mapping for each stage of the customer journey
- Campaign calendars to visualize key activities and dates
- Reporting views and metrics boards for each level of stakeholder
Through the finish line and beyond.
As any marketing leader knows, finding the right software is the first crucial step, but selecting a partner who helps with adoption, training, and ensures you see full ROI is an important second. Our team defines success as you see it and we’re here to take you beyond the finish line.
A unified front
A strong alliance between Marketing and Sales has never been more necessary. Discover a place where customer references, sales, and marketing teams come together.
RO Innovation
Amplify customer references to increase brand awareness and win more deals.